In today's digital landscape, network security is more crucial than ever. Companies are increasingly turning to advanced solutions like the IP Access Controller to safeguard their information. According to a recent report by Cybersecurity Ventures, cybercrime is expected to cost the world over $6 trillion annually by 2021. This staggering figure highlights the urgent need for robust security measures.
Industry expert Dr. Jane Mitchell states, "Investing in an IP Access Controller is no longer optional; it’s a necessity." These devices help manage network access efficiently, ensuring that only authorized personnel can enter sensitive areas. With the rise in remote work, secure access has become a pressing issue for many organizations.
Despite their benefits, many companies still struggle with implementing these access controllers. Security protocols often remain inconsistent. A survey from TechTarget indicates that nearly 60% of firms lack a comprehensive security strategy. This gap can lead to vulnerabilities, underscoring the importance of finding the right IP Access Controller. Organizations must reflect on their current security measures and consider innovative solutions to protect against ever-evolving threats.


When selecting IP access controllers, several key features merit careful consideration. Security should be at the forefront. According to a report by Cybersecurity Ventures, the global cost of cybercrime is projected to exceed $10.5 trillion annually by 2025. Thus, having robust encryption and secure authentication methods is non-negotiable. Look for controllers that support multi-factor authentication. They can significantly mitigate unauthorized access risks by adding extra layers of security.
Scalability is another vital aspect. Organizations evolve. The demand for access control systems must adapt accordingly. Data from MarketsandMarkets indicates that the access control market is expected to grow from $5.4 billion in 2022 to $9.6 billion in 2027. This highlights the necessity of choosing a controller that accommodates future network expansions. Integration capabilities with other security systems are also essential. A seamless combination can enhance overall protection against threats while ensuring user convenience.
User experience cannot be overlooked either. Complicated interfaces can lead to confusion. A study showed that 70% of employees often bypass security measures due to frustration. An intuitive design helps users comply with protocols. Training time should be minimal. The user interface should facilitate easy monitoring and management, allowing swift responses to potential security breaches.
In 2023, the landscape of IP access controllers evolves rapidly. These devices play a vital role in network security. They determine who can access specific areas of a digital network. It’s crucial to analyze the strengths and weaknesses of various brands in this domain.
Some controllers boast advanced integration features. They can connect seamlessly with existing security systems. However, not all controllers offer user-friendly interfaces. Complexity might hinder effective usage. Cost is another consideration. Higher-priced units may not always equate to better security. Some options provide only basic functionalities, leaving gaps in protection.
User experience varies significantly. Some products may promise robust security yet falter in real-world applications. Monitoring access logs can become cumbersome with the wrong system. Obtaining real-time alerts is essential, but not every unit excels in this aspect. Comprehensive data analysis tools are often lacking. Organizations should reflect on these factors when selecting a controller to enhance their network security.
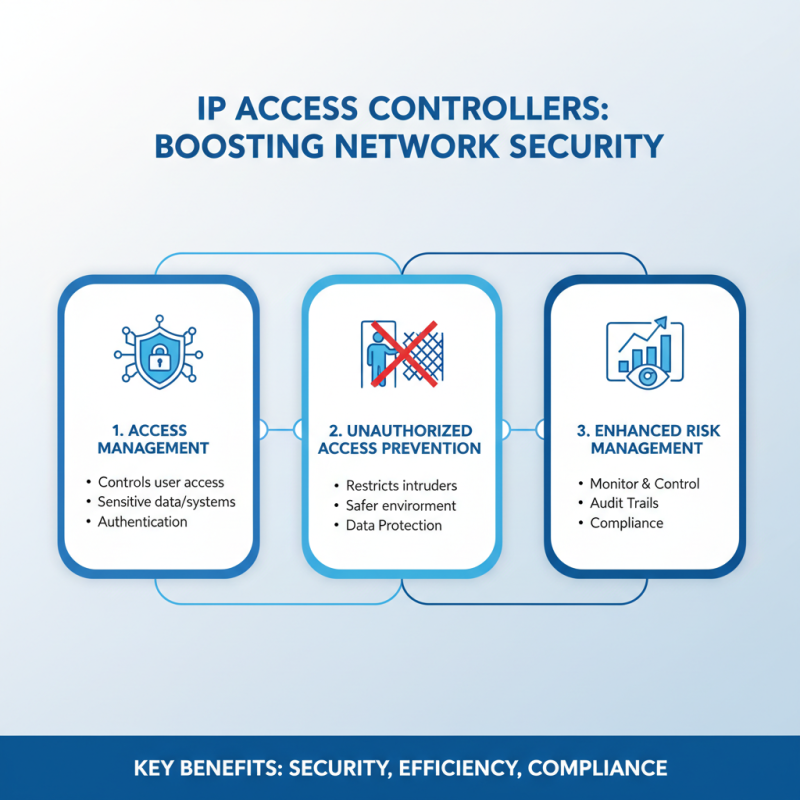
IP Access Controllers play a significant role in enhancing network security. They manage user access to sensitive data and systems. By using these controllers, organizations can restrict unauthorized access effectively. This leads to a safer environment for company resources. Risk management improves when access can be monitored and controlled precisely.
Implementing IP Access Controllers can sometimes present challenges. Configuration errors can occur, potentially exposing sensitive information. Regular audits are crucial to ensure effectiveness. A complex setup can also confuse users, leading to mistakes. Employees must be trained properly on these systems. Otherwise, the benefit of improved security may not be fully realized.
In conclusion, the right IP Access Controller can strengthen security measures. However, organizations must continually assess their systems. Balanced management of security and usability is essential. An approach that focuses on both can provide better protection.
The landscape of IP access control is rapidly evolving. Trends show an increase in the integration of artificial intelligence in security systems. AI-driven solutions are predicted to improve threat detection by over 40%, according to recent industry reports. These technologies analyze patterns in real-time. They adapt to identify anomalies effectively. This adaptability enhances overall security measures.
As more businesses embrace remote access, the demand for cloud-based solutions rises. Reports indicate that cloud-based IP access control systems are expected to grow by 35% in the next year. This trend allows organizations to manage access even from remote locations seamlessly. However, reliance on cloud services raises questions about data security and privacy.
Mobile credentialing is also gaining traction. Users prefer smartphone access over traditional keys. This shift reflects a broader trend towards convenience. Yet, the vulnerability to mobile device hacks cannot be overlooked. Organizations must remain vigilant about potential security gaps. Regular assessments and updates become essential in this changing environment.
The implementation of IP access controllers has transformed network security for many organizations. One case study highlights a medium-sized company that struggled with unauthorized access. They decided to install an integrated IP access control system. This system allowed them to manage entry points effectively, tracking who accessed their network and when. After implementation, the company noticed a significant decrease in security breaches.
In another instance, a school district faced challenges with managing access to sensitive information. They opted for a solution that centralized their control processes. Staff members were given secure access based on their roles. However, initial training was insufficient, leading to confusion among staff. Still, they persevered, identifying gaps in knowledge, and improved their training sessions. This reflected the importance of user education in maximizing security systems' effectiveness.