In an age where security is paramount, choosing the right technology is crucial. The Ip Access Controller stands at the forefront of this evolution. This device allows businesses and homes to manage entry points effectively. Enhanced control and security are not just options; they are necessities.
When selecting an Ip Access Controller, you should consider both function and reliability. Different models offer various features, catering to distinct needs. Some may excel in easy integration, while others focus on advanced biometric capabilities. It's easy to overlook specific requirements. Focusing on features alone might cause firms to miss what fits their environment best.
Investing in an Ip Access Controller could be a transformative step for security management. Yet, it also invites questions and challenges. Are these systems foolproof? Can they adapt to evolving threats? Reflection on past implementations can provide valuable insights. Choosing the best controller involves weighing all aspects carefully.
The landscape of IP access control technology is rapidly evolving. In 2026, companies are increasingly focusing on integration and interoperability. This shift allows multiple security systems to work seamlessly. Enhanced connectivity will be a key trend. Devices will sync more efficiently, resulting in smoother operations.
Artificial intelligence plays a pivotal role in this development. It enables more accurate identification of individuals via facial recognition. With time, this technology may refine its accuracy, but challenges remain. False positives can occur, raising concerns about privacy.
Mobile access control is another crucial trend. Users will prefer smartphones over key cards. This approach enhances convenience but introduces potential security gaps. There is a balance to strike. As innovations emerge, organizations must remain vigilant about vulnerabilities. Adapting technology while ensuring robust security is a complex task. Reflection on these aspects is essential for developing reliable solutions.
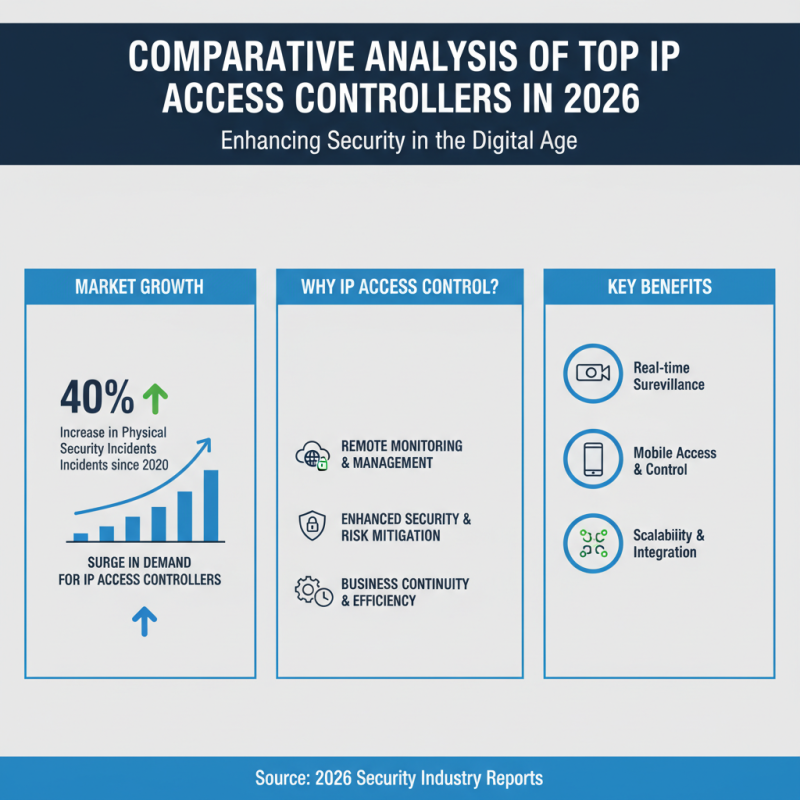
In 2026, the demand for IP access controllers has surged. Security is a top concern for businesses, with several reports indicating that physical security incidents have risen by 40% since 2020. Organizations are increasingly investing in IP access control systems to mitigate these risks. These systems provide remote monitoring and management, which enhances security.
A recent study showed that 70% of companies prefer IP-based solutions due to their flexibility. These systems integrate with existing networks, offering a seamless installation experience. However, not all IP access controllers are created equal. Some may lack user-friendly interfaces, hindering effective management.
When analyzing the top models, performance might vary significantly. It's crucial to assess scalability, as companies often underestimate future expansion needs. A staggering 50% of users reported difficulties in scaling their existing systems. Failing to anticipate growth can lead to unnecessary expenses and security vulnerabilities. Each choice requires careful consideration.
The integration of IoT technology into IP access control systems is transforming security features. According to a recent report by MarketsandMarkets, the global market for IoT in access control is projected to reach $6.3 billion by 2025. This surge is driven by the growing need for advanced security and real-time monitoring.
With IoT, access control systems can now provide data analytics for behavior patterns and potential security threats. For example, smart locks can communicate with surveillance cameras, enabling instant alerts for unauthorized access. Yet, this increased connectivity raises concerns. Cybersecurity threats loom larger. The 2023 Verizon Data Breach Investigations Report noted that 45% of breaches involved IoT devices.
Integration complicates security management. It presents new vulnerabilities. Organizations must regularly update their security protocols, adding to operational costs and complexity. Many are unprepared for these challenges. A study by Ponemon Institute showed that 61% of companies lack adequate resources for IoT security. It's clear that while IoT enhances access control, it simultaneously demands careful scrutiny and proactive measures.
| Model | IoT Integration | Security Features | User Capacity | Additional Features |
|---|---|---|---|---|
| Model A | Yes | Biometric Access, Encryption | 500 Users | Remote Management, Real-time Notifications |
| Model B | No | Standard Keycard | 300 Users | Scheduled Access Control |
| Model C | Yes | Facial Recognition, 2-Factor Authentication | 1000 Users | Visitor Management, Audit Trails |
| Model D | Yes | Mobile App Access, Advanced Encryption | 1500 Users | Integration with Fire Alarms |
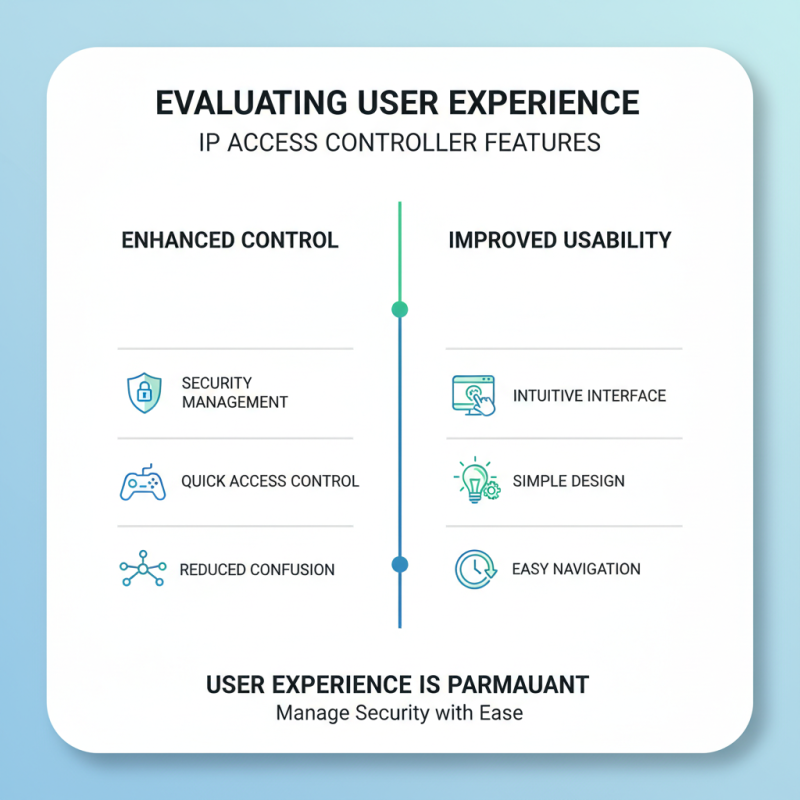
When evaluating an IP access controller, user experience is paramount. Features that enhance control and usability can significantly impact security management. Look for an intuitive interface. A simple design makes navigation easy. Users can manage access quickly, reducing confusion.
Tips: Always test the software before full implementation. Ensure that all features function as advertised. Customization options are essential. Flexibility allows users to tailor settings to their needs. Users prefer systems that adapt to their workflows.
Real-time monitoring is another critical feature. This enhances security and enables quick responses. Alerts should be straightforward and informative, not overwhelming. Inefficient notifications can cause frustration. It's important to find a balance between vigilance and user comfort. Consider feedback from users to refine these aspects.
In 2026, the need for robust security solutions continues to grow. IP access controllers offer significant advantages for businesses aiming to enhance safety. However, a cost-benefit analysis is essential before implementation. An initial investment might seem daunting. Yet, the long-term savings in potential theft and data breaches can offset these costs.
The effectiveness of IP access controllers lies in their ability to streamline security. They create restricted access areas and allow remote monitoring. This not only secures physical premises but also safeguards critical data. However, organizations must consider installation and maintenance expenses. A poorly executed installation can lead to vulnerabilities. Regular updates are necessary to ensure optimal performance.
Moreover, user training is crucial for maximizing effectiveness. Employees must understand how to operate the systems properly. Some might experience resistance or confusion at first. The learning curve can impact productivity initially. Yet, with time, the benefits often outweigh these initial setbacks. Enhanced security can lead to increased customer trust, ultimately boosting revenue for businesses.







